
Instant Active Directory Replication
A lot of people think 15 minutes is the fastest AD can replicate between sites. It’s not. Here’s how to enable change notification and a script to audit your environment.

A lot of people think 15 minutes is the fastest AD can replicate between sites. It’s not. Here’s how to enable change notification and a script to audit your environment.

After 16 years on WordPress, I’ve moved the blog to Hugo with the PaperMod theme, hosted on Azure Static Web Apps. Here’s why.

Claude Code has changed how I do infrastructure work. Here’s how I use it, and a commitment about AI-generated content on this blog.
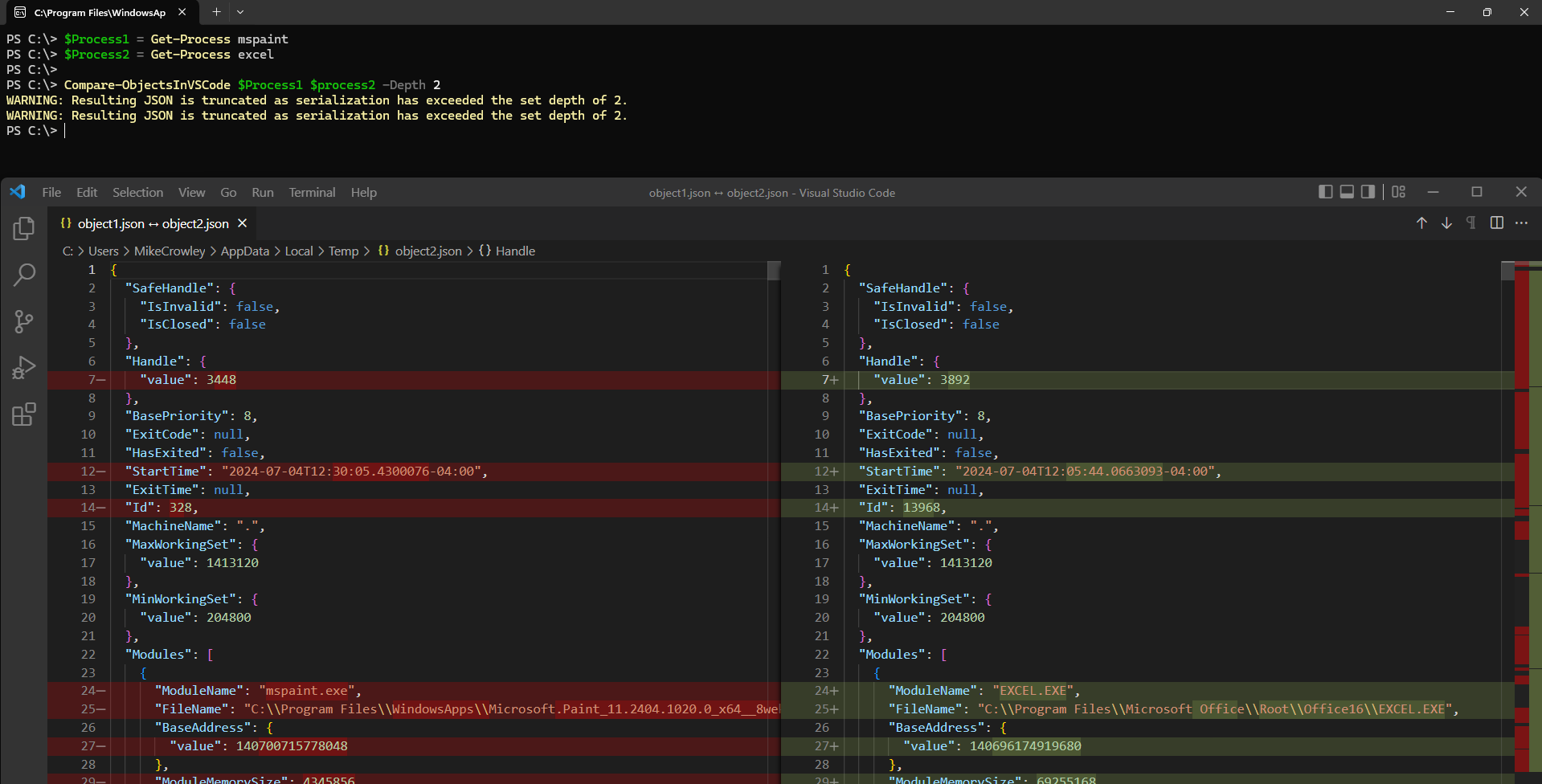
PowerShell’s Compare-Object is great for programmatic comparisons, but VS Code offers a better visual experience for complex objects.
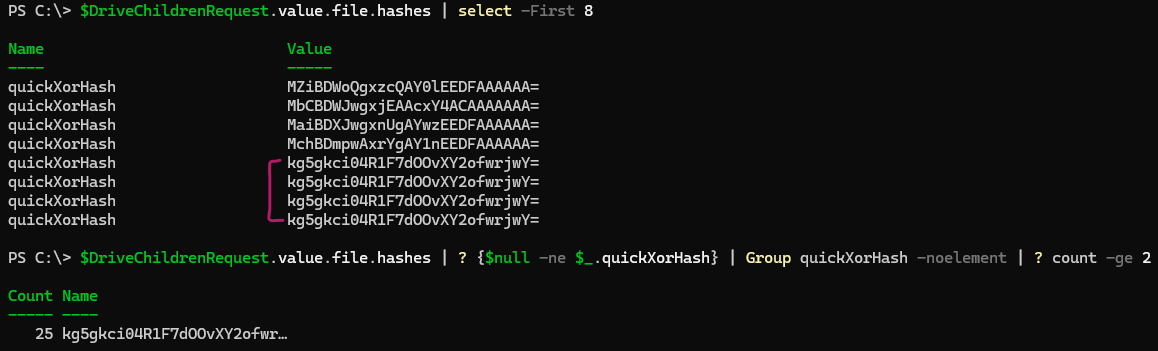
Learn how to use the quickXorHash property in Microsoft Graph to identify duplicate files across OneDrive and SharePoint Online.